In the rapidly advancing digital age, the internet has become an integral part of our daily lives, transforming the way we communicate, work, and share information. However, with this convenience comes a dark underbelly – the proliferation of fake documents online. Cybersecurity, once confined to protecting networks from external threats, now extends its reach to safeguarding against the dangers posed by counterfeit documents circulating in the virtual realm.
The Rise of Fake Documents:
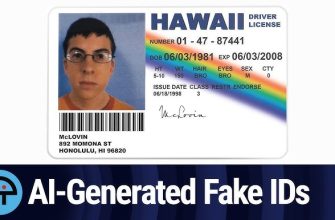
The internet provides a breeding ground for various forms of cybercrime, and the creation and distribution of fake documents have become a lucrative venture for cybercriminals. From counterfeit identification cards and passports to forged academic certificates and financial statements, the digital space has become a haven for those seeking to deceive and exploit.
- Identity Theft: One of the most significant dangers associated with fake documents online is the facilitation of identity theft. Cybercriminals can use forged identification documents to impersonate individuals, gaining unauthorized access to sensitive information, financial accounts, and even committing crimes in the victim’s name.
- Phishing and Social Engineering: Fake documents serve as powerful tools for phishing attacks and social engineering scams. Fraudulent emails or websites often employ counterfeit documents to trick individuals into providing personal information, such as login credentials, credit card details, or social security numbers.
- Malware Distribution: Cybercriminals may embed malicious software within fake documents, using them as vehicles to spread malware. Opening seemingly innocuous files can lead to the installation of harmful software, compromising the security of personal and organizational data.
- Fraudulent Transactions: The prevalence of counterfeit financial documents online poses a significant risk to businesses and individuals alike. Fake invoices, receipts, and financial statements can be used to facilitate fraudulent transactions, leading to financial losses and reputational damage.
Combatting the Threat:
Given the pervasive nature of fake documents online, it is crucial to implement robust cybersecurity measures to mitigate the risks associated with their use. Here are some strategies to combat this growing threat:
- Document Verification Tools: Implementing advanced document verification tools can help organizations and individuals verify the authenticity of documents. These tools use advanced algorithms and technologies to detect inconsistencies and irregularities in the structure and content of documents.
- User Education and Awareness: Educating users about the risks associated with fake documents is essential. Training programs and awareness campaigns can help individuals recognize and report suspicious documents, reducing the likelihood of falling victim to scams.
- Multi-Factor Authentication (MFA): Employing MFA adds an extra layer of security by requiring multiple forms of identification before granting access to sensitive information. This can help prevent unauthorized access, even if fake documents are presented.
- Regular Security Audits: Conducting regular security audits can help organizations identify vulnerabilities in their systems and processes. This proactive approach allows for the detection and rectification of potential security threats before they can be exploited.
As we navigate the digital landscape, the dangers posed by fake documents online demand our attention and vigilance. Cybersecurity measures must evolve to combat the ever-growing sophistication of cybercriminals who exploit the ease of document forgery in the virtual realm. By staying informed, implementing advanced security measures, and fostering a culture of cybersecurity awareness, we can collectively defend against the perils of fake documents and create a safer digital environment for all.