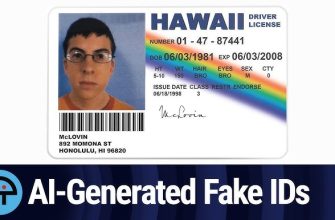
As technology advances, so does the sophistication of fraudulent activities, particularly in the realm of fake documents. Whether in personal or professional settings, the ability to recognize and thwart counterfeit documentation is crucial for protecting against identity theft, financial fraud, and other deceptive practices. This article aims to provide individuals and businesses with insights into recognizing fake documents and implementing effective fraud protection measures.
- Document Authentication Features:Legitimate documents often incorporate various security features that are challenging to replicate. When examining documents such as identification cards, passports, or banknotes, be vigilant for features like holographic images, watermarks, microprinting, and UV features. Familiarize yourself with the authentic characteristics of commonly used documents to identify inconsistencies.
- Verify Watermarks and Security Threads:Watermarks and security threads are common security features in official documents. Hold documents up to the light to check for embedded watermarks or security threads. These features are usually woven into the paper and can be challenging for counterfeiters to reproduce accurately.
- Check for Microprint:Microprinting involves tiny text or patterns that are difficult to replicate with standard printing techniques. Authentic documents often contain microprint that is visible under magnification. Use a magnifying glass to inspect text and patterns, especially on currency, identification cards, and official certificates.
- Examine Fonts and Typography:Pay attention to the fonts and typography used in documents. Legitimate documents maintain a consistent and professional appearance, whereas fake documents may exhibit irregularities in font size, style, or spacing. Inconsistencies in typography can be a red flag for potential fraud.
- Consistency in Design and Layout:Authentic documents adhere to a consistent design and layout. Check for uniformity in the placement of logos, seals, and other graphical elements. Any deviation from the standard design may indicate a counterfeit document.
- Quality of Printing:Counterfeit documents often lack the precision and high-quality printing found in legitimate counterparts. Look for signs of pixelation, blurriness, or irregularities in the printing process, especially in areas where intricate details are present.
- Scrutinize Signature Authenticity:Genuine signatures typically exhibit consistent characteristics. When verifying signatures on documents, look for natural flow, pen pressure variations, and other distinctive features. Compare signatures to known authentic samples whenever possible.
- Use Technology for Verification:Leverage technological tools and apps designed for document verification. Many official documents now come equipped with QR codes or other machine-readable features that can be authenticated using specialized apps. Additionally, online tools and databases may offer verification services for certain types of documents.
- Be Skeptical of Unusual Requests:Stay alert to unusual or unexpected requests for personal information or documentation. Scammers may use fake documents to support fraudulent activities such as phishing scams, identity theft, or financial fraud.
- Seek Professional Assistance:
When in doubt, seek the expertise of professionals. Legal and forensic document experts can provide thorough analyses to determine the authenticity of documents, especially in cases where substantial financial or legal implications are involved.
Recognizing fake documents is an essential skill in the digital age, where deceptive practices continue to evolve. By staying informed about the security features inherent in legitimate documents and remaining vigilant for inconsistencies, individuals and businesses can fortify their defenses against the pervasive threat of fraudulent documentation. Combining these strategies with technology and professional expertise creates a comprehensive approach to fraud protection, fostering a safer and more secure environment for everyone.